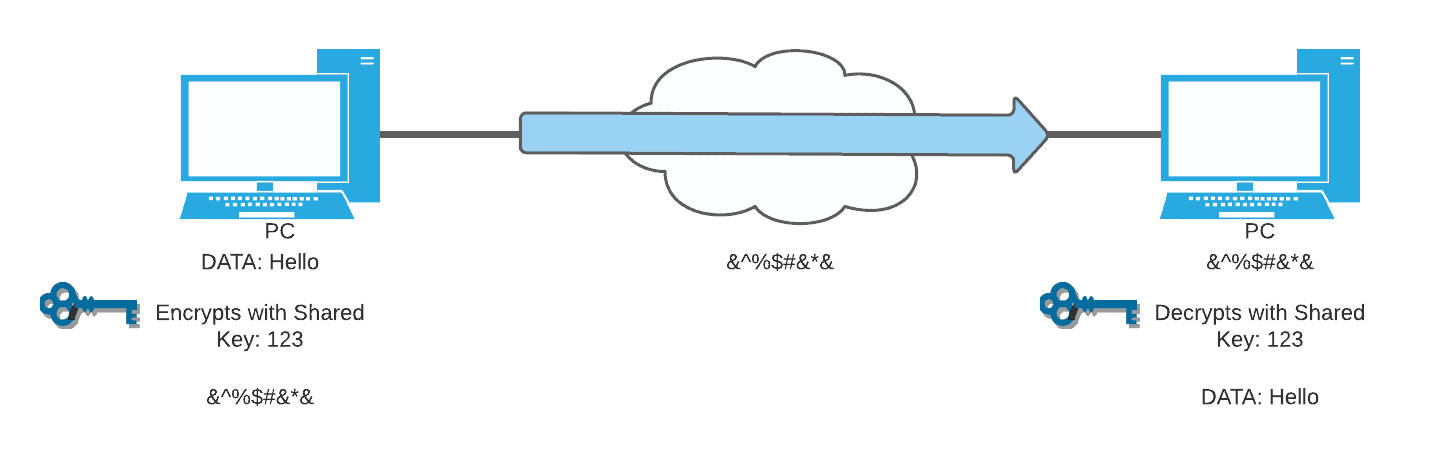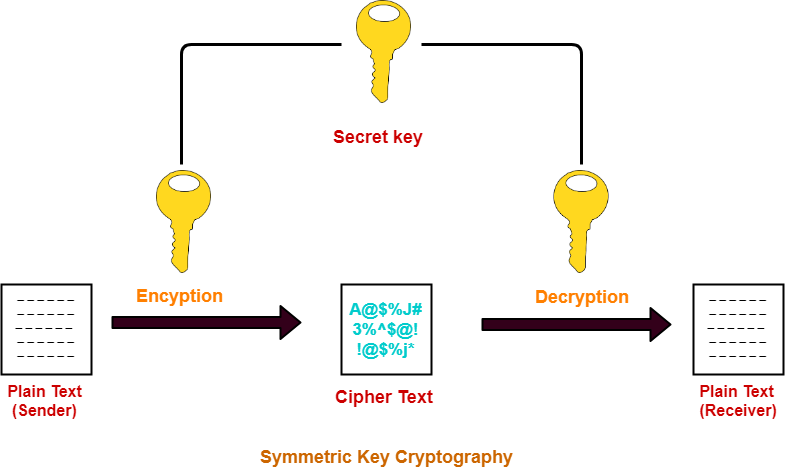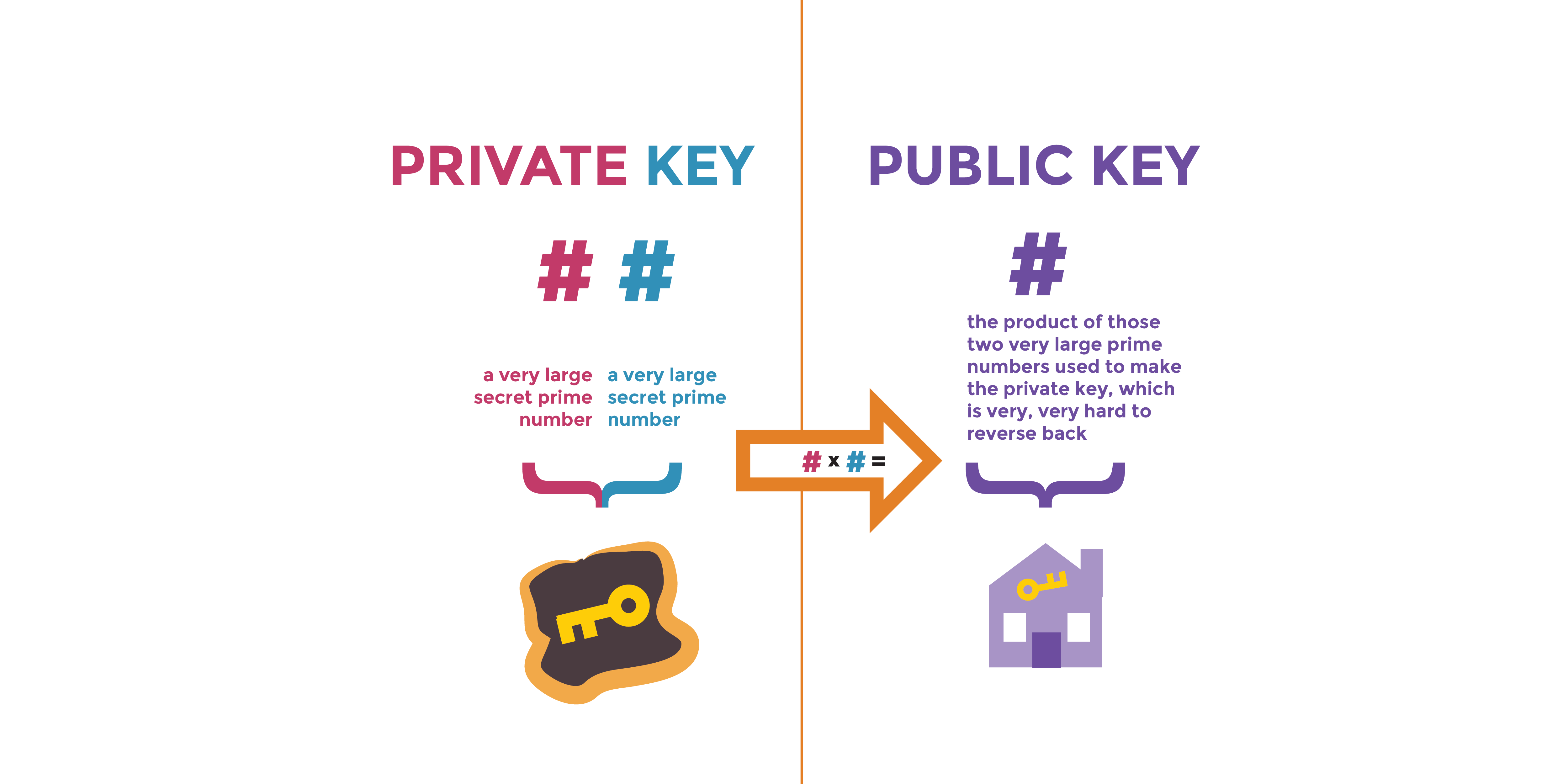
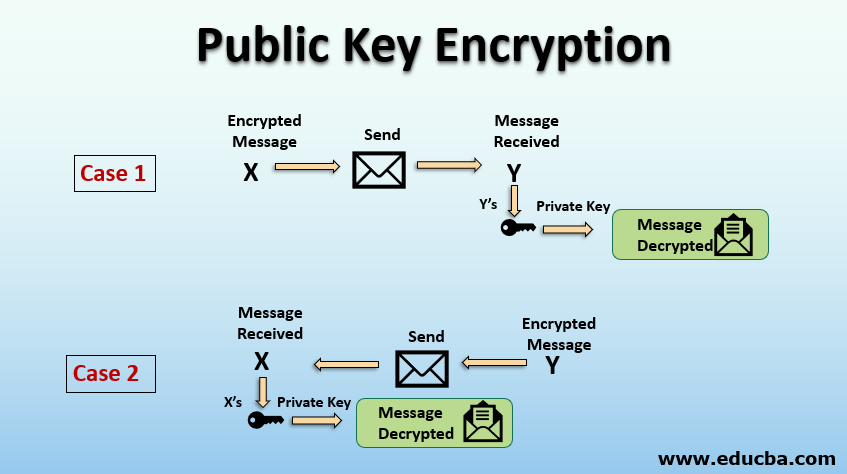
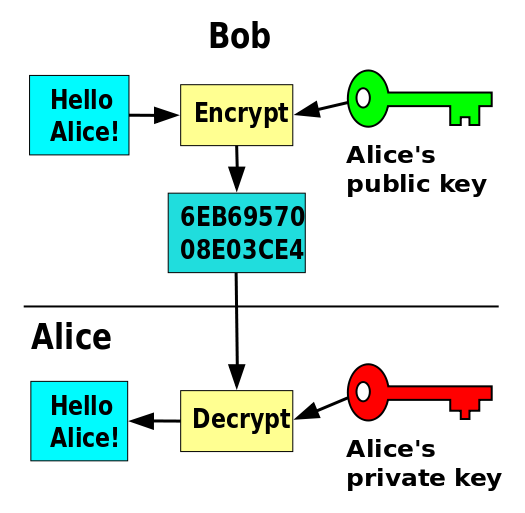
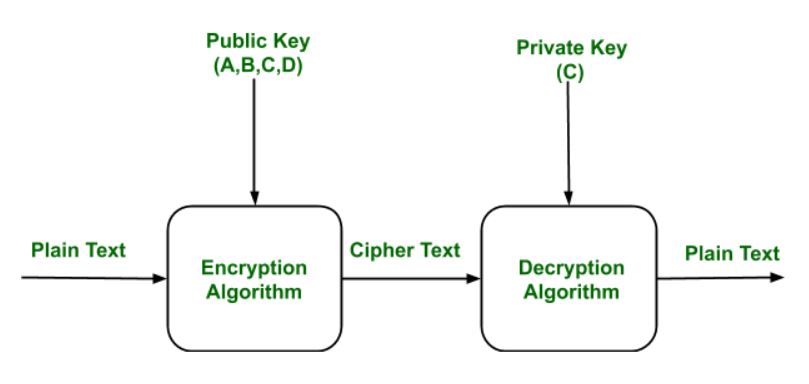
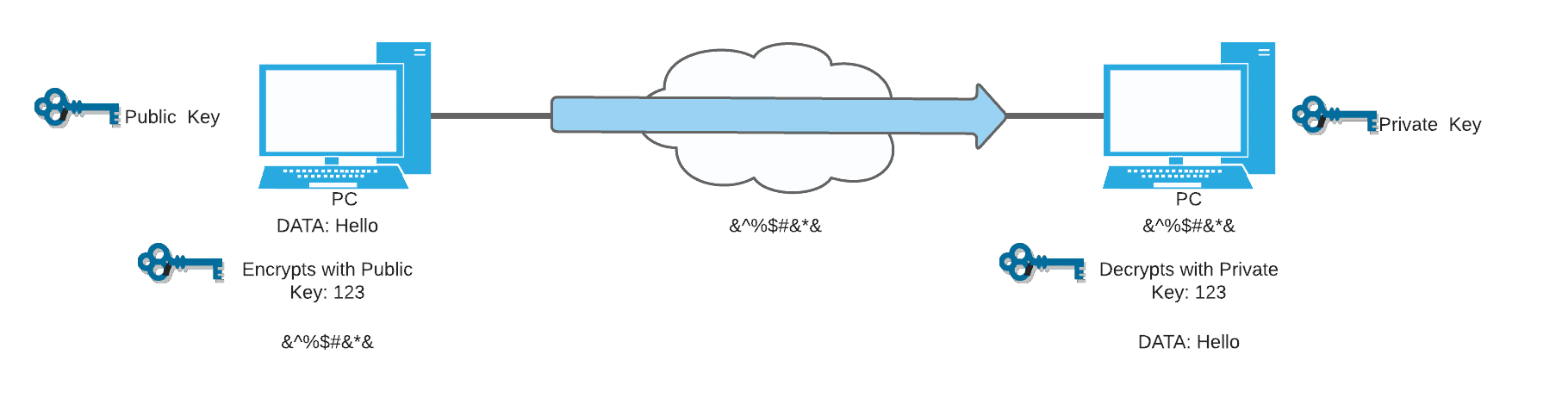
A Deep Dive on End-to-End Encryption: How Do Public Key Encryption Systems Work? | Surveillance Self-Defense
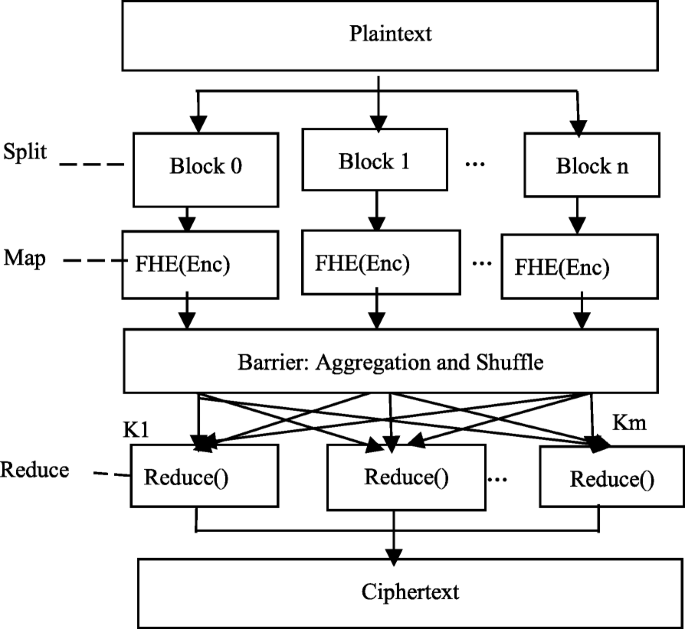
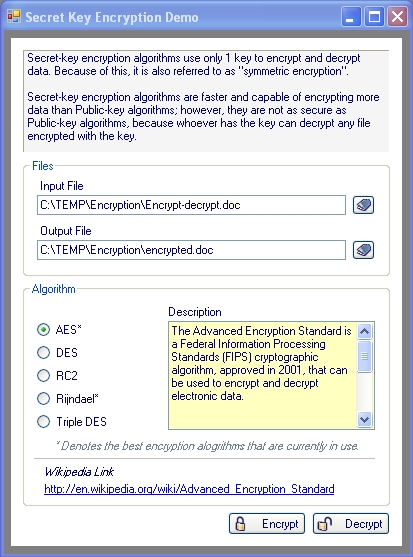
A privacy protection-oriented parallel fully homomorphic encryption algorithm in cyber physical systems | EURASIP Journal on Wireless Communications and Networking | Full Text
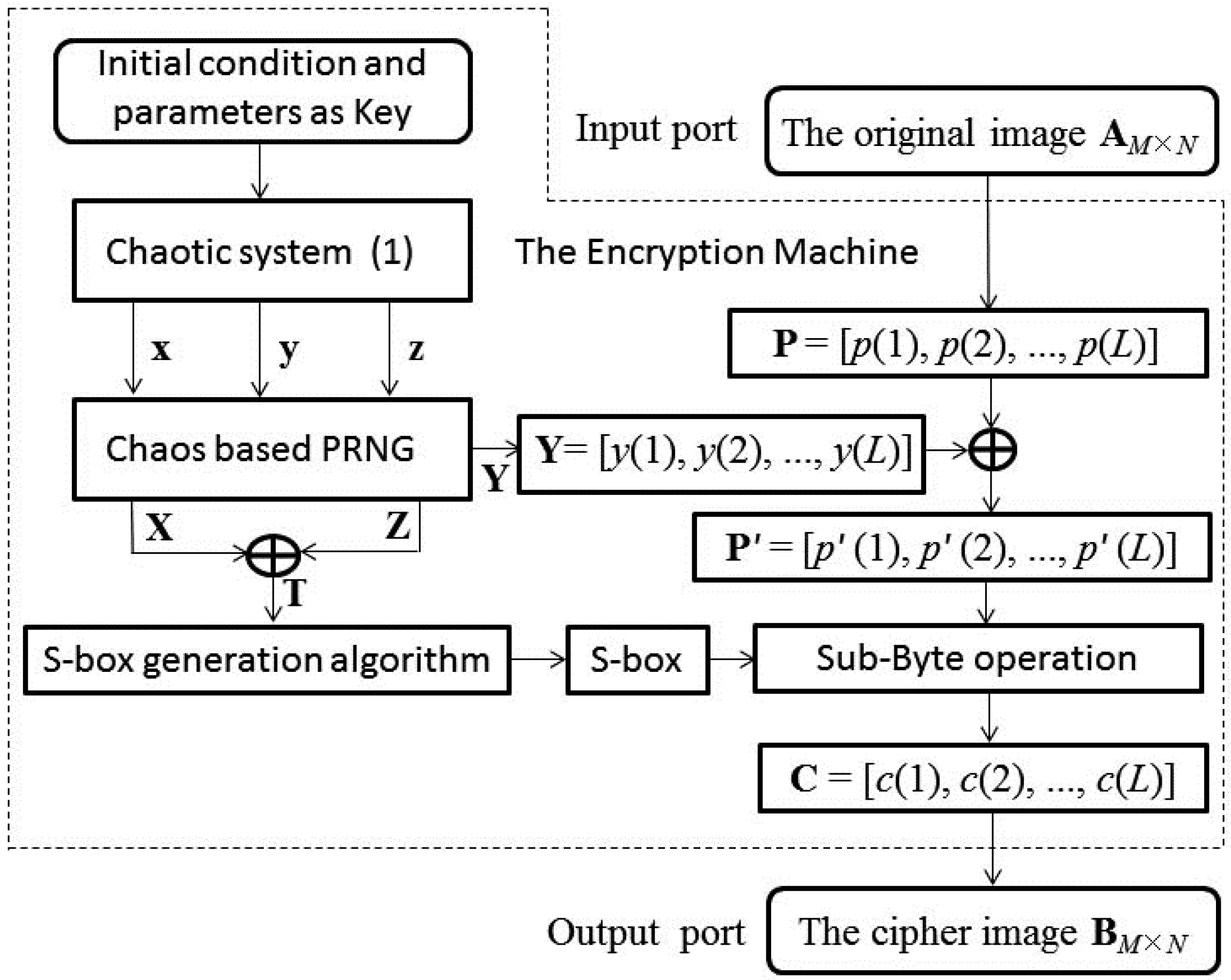
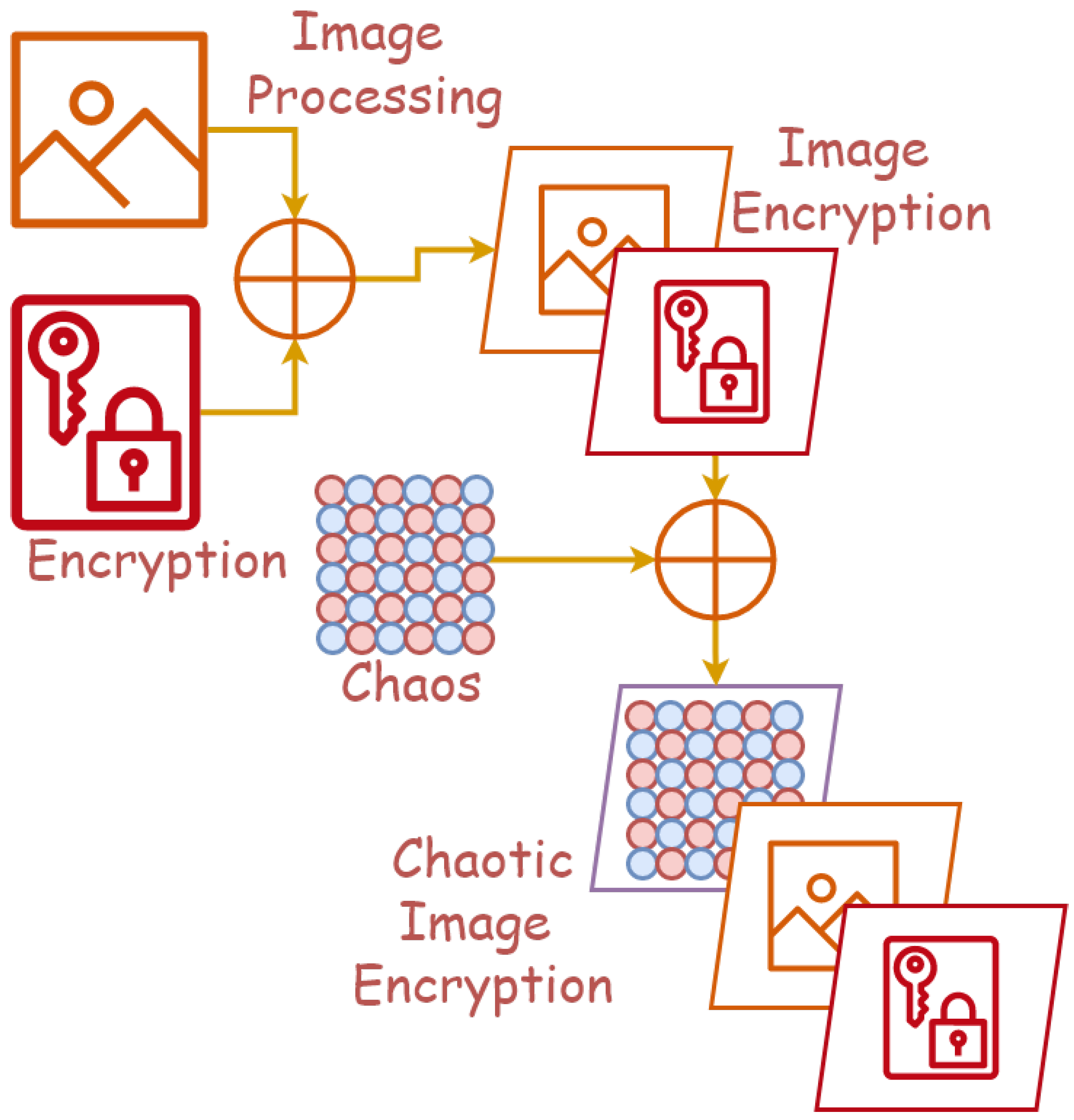
Symmetry | Free Full-Text | Cryptanalysis and Improvement on an Image Encryption Algorithm Design Using a Novel Chaos Based S-Box
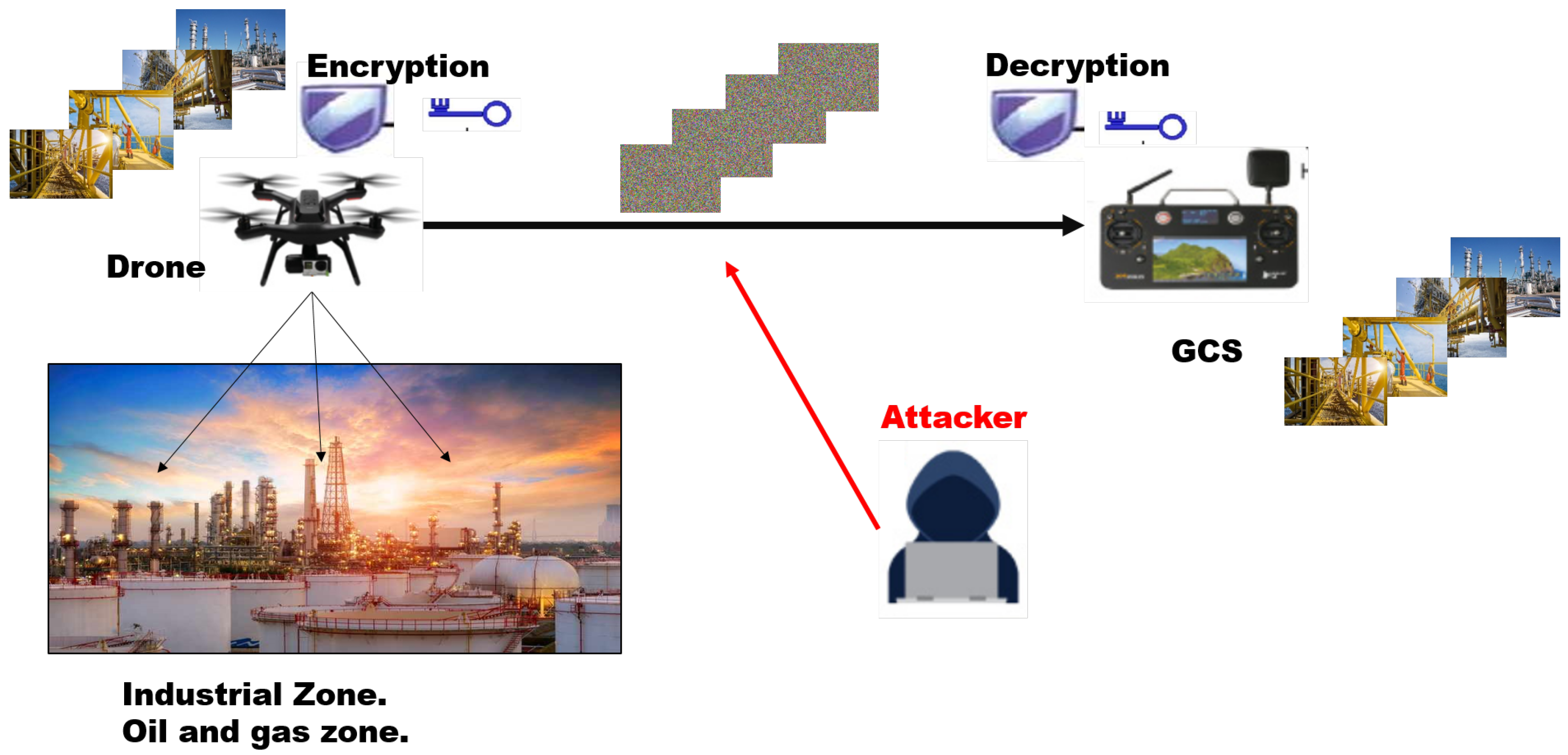
Drones | Free Full-Text | A New Image Encryption Algorithm Based on DNA State Machine for UAV Data Encryption

Using the proposed method, the floating frequency of the encrypted signal | Download Scientific Diagram


![PDF] Image Encryption based on Floating-Point Representation | Semantic Scholar PDF] Image Encryption based on Floating-Point Representation | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f6c92caa05be7fe95a99ba6597ae00b6208daa77/6-Figure1-1.png)







![PDF] Image Encryption based on Floating-Point Representation | Semantic Scholar PDF] Image Encryption based on Floating-Point Representation | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f6c92caa05be7fe95a99ba6597ae00b6208daa77/7-Figure3-1.png)